The Beale Ciphers are often presented as a finished story, waiting only for its final step.
A man named Thomas J. Beale is said to have traveled west in the early 19th century, discovered a large quantity of gold and silver, and arranged for it to be buried in Virginia. Before leaving, he placed a box with a trusted acquaintance, to be opened only if he failed to return.
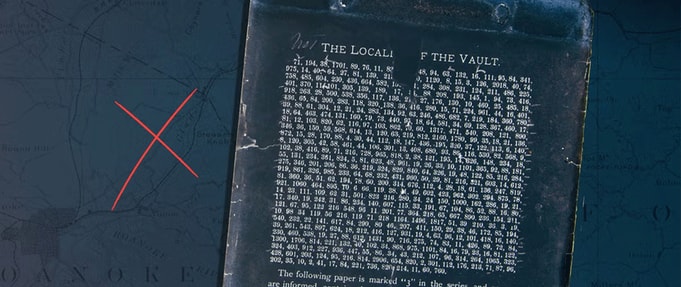
Inside were three encrypted texts. One would describe the treasure's location. Another would list its contents. The third would name those entitled to it. If all three could be read, the story would resolve itself.
That is how the tale is usually told. It arrives already shaped, with nothing obviously missing except the solution.
Trying to Find the Beginning
The difficulty starts when you try to move back from the story to the point where it begins. Everything rests on a single publication, a pamphlet printed in 1885. It presents itself as an account of earlier events, supported by documents that had been held in private hands.
The narrative is framed as something passed down, then finally released. Beyond that pamphlet, there is very little to work with. No original letters that can be examined independently. No clear historical record of a Thomas J. Beale that matches the description given. No contemporary reference to the expedition or the burial of the treasure.
What exists is the printed version, appearing decades after the fact, with nothing solid sitting behind it that can be confirmed. That absence does not settle the question. But it does set the limits of what can be known.
The Cipher That Gives an Answer and the Two That Remain Closed
One of the three ciphers can be read. The second cipher is said to use the Declaration of Independence as a key. When the numbers are matched to words in that text, a message appears. It describes the treasure in practical terms. Quantities of gold and silver. Jewels. Enough detail to make the claim feel concrete.
It works, in the sense that it produces readable English. That alone has been enough to convince many that the system as a whole must be sound. At the same time, it raises its own questions.
The decoded message does not lead to the treasure. It only describes it. It confirms that something is there but offers no way to find it. In that respect, it does exactly what the story needs it to do. It gives substance without resolution.
There is also the matter of how neatly it works. The Declaration of Independence is an obvious key, widely available by the time the pamphlet appeared. Whether that points to a genuine method or a constructed one is difficult to say.
The other two ciphers do not yield in the same way. Cipher number one, which is supposed to describe the location, and cipher number three, which should identify the heirs, remain unread. Throughout time, they have been examined repeatedly, using a range of approaches.
Some attempts have focused on alternative texts as keys. Others have looked for patterns within the numbers themselves. More recent efforts have applied computational methods to search for structures that might not be visible at first glance. Nothing has held.
There have been moments where a solution seemed close, or at least plausible. These tend not to last long under scrutiny. What appears convincing at first begins to lose coherence when examined more closely. The two unsolved ciphers remain in place, unchanged.
What the Pamphlet Is Doing
The 1885 pamphlet did more than present the ciphers. It constructs the entire framework in which they make sense— providing the narrative of Beale himself, the journey west, the discovery of wealth, and the decision to bury it. It introduces the intermediary who receives the box and waits for instructions that never come. It explains why the ciphers exist and why they have not already been solved.
Without that framing, the ciphers would be little more than columns of numbers. With it, they become something else. A problem with stakes. A story that invites continuation. That is worth keeping in mind. The ciphers do not arrive on their own. They arrive already explained.
A Familiar 19th-Century Shape
By the time the pamphlet appeared, the broader culture was already receptive to this kind of story. Hidden treasure narratives were common. The American landscape, particularly the idea of the frontier, had taken on a quality that made such stories plausible. Lost wealth, concealed in moments of danger, waiting to be recovered, was a familiar theme.
Printed pamphlets offered a way to circulate these accounts with a degree of authority. They could present themselves as documentary, even when the line between record and invention was unclear. The Beale story fits that pattern without strain. It does not stand out as an isolated curiosity. It sits comfortably among other narratives of the same general type.
Part of the reason the Beale Ciphers persist is that they remain unresolved. If all three messages had been decoded, the story would likely have come to an end. Either the treasure would have been found, or it would not. In either case, the interest would diminish.
Instead, the situation remains open. One cipher works. Two do not. That is enough to suggest that a solution exists, but not enough to make it accessible. Each new attempt to break the codes becomes part of the story itself.
People approach it from different angles, bring different assumptions, and try different methods. Most of these efforts fade, but they leave a trace behind them. Another layer added to what is already there. The ciphers continue to invite attention without ever quite rewarding it.
What Can Be Confirmed
There is no verified location for the treasure. There is no recovered cache that can be linked to the story. There is no independent record that clearly places Thomas J. Beale within a framework that matches the events described.
There is, however, a printed pamphlet, a set of numerical ciphers, and a long history of attempts to connect them to something tangible. That may be enough to account for the story’s survival.
It is possible that something lies behind the Beale Ciphers. A smaller story, perhaps, that has been expanded over time. It is also possible that the entire account was constructed to appear convincing, with just enough internal logic to sustain it. There is no clear point at which one explanation gives way to the other.
What remains is a narrative built around absence. Missing documents, missing verification, missing resolution. The ciphers promise access to something hidden, but never quite provide it. That, in itself, may be the reason the story endures. It does not need to be solved. It only needs to remain just out of reach.
Featured image: Wiebke Elzel / 2024 Artists Rights Society